Ship 2.0 Privacy and Data Security¶
Ship 2.0 is a client / server system for interacting with GitHub Issues. This document describes where, how, and why your data is collected, transmitted, and stored when using Ship 2.0. For more information about our site and service policies, please see our Terms of Service.
While we make every reasonable effort to ensure that your data remains private and secure while using Ship, we understand that this goal is to some degree in tension with convenience and usability, and furthermore that despite our best efforts we recognize that bugs or mistakes may happen. As with any software, it’s ultimately up to you to decide if it makes sense to use given your personal or organizational tolerance for risk.
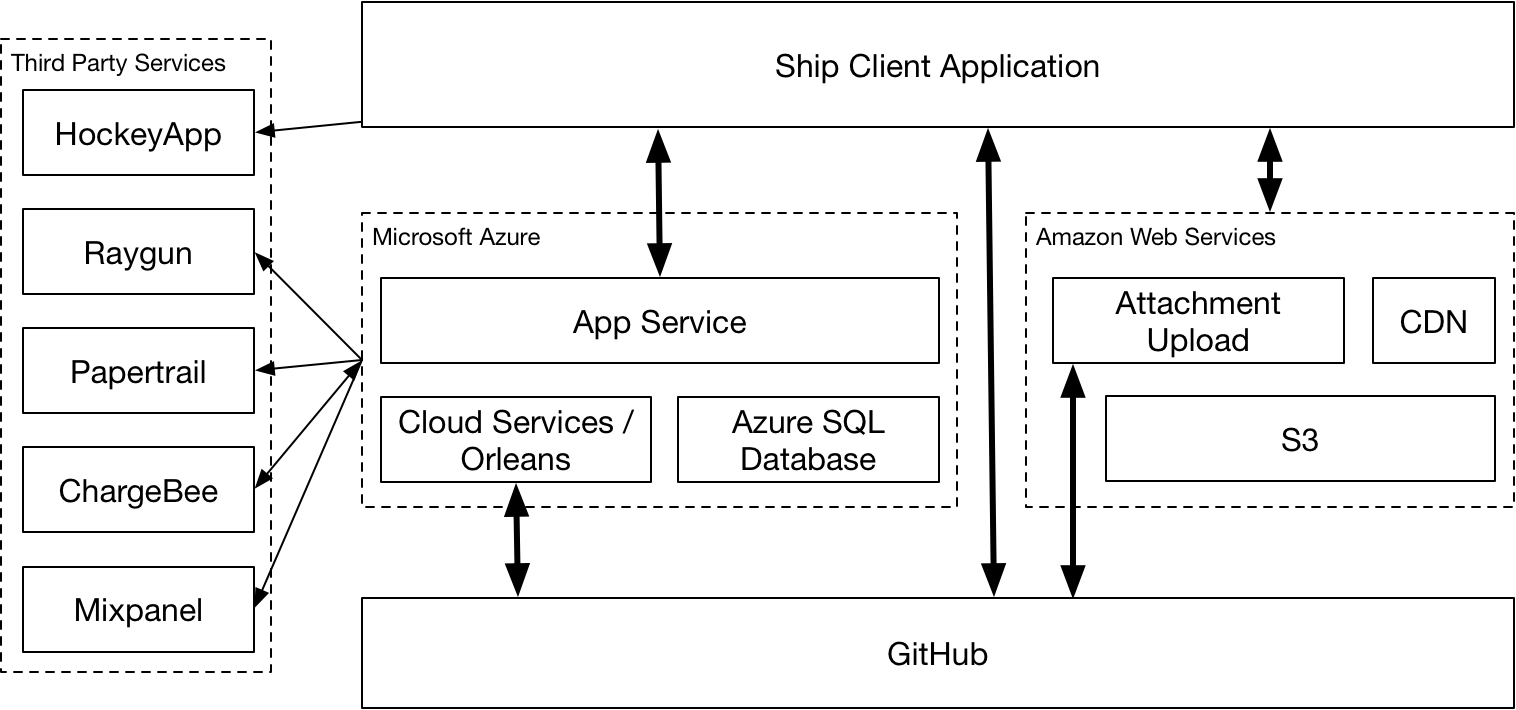
System Overview¶
Ship provides a user queryable database of all of your GitHub Issues and associated metadata, such as repositories, users, organizations, labels, milestones, events, comments, and notifications. This database is stored locally on your computer, remotely on Real Artists’s infrastructure running in Microsoft Azure, and finally in GitHub.
Ship Client¶
The Ship client application authenticates directly with GitHub using OAuth. Your GitHub password and/or two factor access code is never transmitted to anyone except GitHub directly, and it isn’t stored anywhere on your computer by Ship. Once an OAuth token is received from GitHub, this is used for all communications between Ship client and Ship server, as well as all communications between Ship client and GitHub directly. Your GitHub OAuth token is stored securely on your computer in your local login keychain.
Ship client primarily communicates with the Ship server running in Azure for most regular functions. For some operations, Ship client will talk directly to GitHub.
Ship client is subject to Apple’s App Transport Security, which forces it to communicate with all outside services via secure connections.
Ship client stores its local copy of your issues on your computer at ~/Library/RealArtists/Ship2.
Ship Server¶
The primary purpose of Ship server is to provide clients with real time push updates and fast bulk and incremental data synchronization.
The Ship server discovers and stores GitHub Issues belonging to any GitHub repositories to which you have push access. It also stores associated metadata queried from the GitHub API, including details about repositories, users, organizations, milestones, labels, and events. GitHub’s permissions system is consulted and respected: the information Ship server knows and will disclose to you is a subset of the information that github.com will disclose to you. Ship server only collects from GitHub the minimum amount of information needed to support Ship’s feature set.
All communications between Ship server and GitHub as well as the third party services that it uses are secured with TLS1.2.
The Ship server database is encrypted at rest by Azure SQL Transparent Data Encryption. This includes backups as well.
Attachment Service¶
Ship provides a file attachment hosting service running in Amazon Web Services. When you ask to attach a file or media to an issue in Ship, the attachment services first verifies your GitHub OAuth token, then it securely generates a 128 bit random identifier to prevent guessing the attachment URL, and finally provides a pre-signed upload URL for the client to upload the attachment to a dedicated bucket in Amazon S3. The only way to download an attachment from the service is to know its exact URL containing the 128 bit random identifier embedded in the body of an issue or comment.
A guide to GitHub data as used by Ship¶
Ship 2.0 uses OAuth to request permission to access your GitHub data. The following GitHub OAuth scopes are requested: user:email,repo,admin:repo_hook,read:org,admin:org_hook. You can read more about what these OAuth scopes grant in the GitHub OAuth Documentation.
For each GitHub scope requested, the list below describes why Ship requests it and what it does with the data.
user:email: Ship uses this information to learn who you are, including your GitHub user id, user login, and associated email. Your email address is used to address your receipts if you opt to purchase a subscription to Ship, and we may use it to contact you with help or critical information about the Ship service, but aside from that we don’t use it or share it with any third parties for any reason.repo: Repository scope is required to interact with GitHub Issues in private and public repositories. In general, Ship’s server environment does not access or store your source code, with the exception that it does access any issue templates that your repositories may contain. The Ship client application will access your source code in order to display GitHub Pull Requests, but this communication is performed directly between your computer and GitHub.read:org: GitHub organization membership is used to determine your eligibility to purchase or modify an organization wide site license for Ship.admin:repo_hookandadmin:org_hook: If possible, repository and organization hooks are installed in order for GitHub to be able to push events to Ship’s server. Any events related to issues or metadata surrounding issues such as milestones, labels, or new repositories that may contain issues are observed. Additionally, pushes to repositories are observed, but only in order to detect changes to any ISSUE_TEMPLATE files.
Third Party Services Used¶
Microsoft Azure¶
The main Ship server application and database runs in Microsoft Azure.
Amazon Web Services¶
The attachment service is used to allow you to upload and host files and media attachments in your issues and comments runs in AWS.
Papertrail¶
Papertrail is used to log service information from the Ship server application running in Azure. The purpose of these logs are primarily to help us debug the service. We don’t log any private information to Papertrail such as OAuth tokens, email addresses, or raw HTTP responses. We do log the following information:
- User IP addresses
- GitHub URLs (which may include github login names and repository names)
- HTTP response sizes
- Numeric GitHub identifiers
- Internal error messages and debugging information
Raygun¶
Raygun is used to log any errors that occur in Ship server. Like with Papertrail, we don’t include any private information in these error reports, but we may include information such as IP addresses, GitHub URLs and GitHub login names and numeric identifiers in order to help us debug issues.